Threat Hunting: Key Takeaways
- Threat hunting is classified into three main types: structured, unstructured, and situational
- Successful threat hunting unfolds in three key phases: trigger, investigation, and resolution
- The frequency of threat hunting should align with your risk exposure and industry standards
In 2024, organizations patched just 54% of known vulnerabilities in perimeter devices, leaving nearly half unaddressed and creating a broad attack surface for threat actors.
Patch management is important, but it only goes so far. Real protection comes from hunting threats before they strike.
Threat hunting is a proactive cybersecurity approach focused on identifying and mitigating hidden threats within a network before they can cause significant damage.
To help you understand how threat hunting strengthens your security posture, we will help you:
- Understand the main types of threat hunting and how each approach works
- Break down the threat hunting process
- Explore key differences between threat hunting and threat detection
- Discover trusted threat hunting services available through Forgepath
Types of Threat Hunting
When it comes to tracking down hidden threats, experts typically take one of three main approaches, each with its own strategy, starting point, and level of proactivity.
These include:
- Structured hunting: A hypothesis-driven approach where analysts proactively search for adversary tactics, techniques, and procedures (TTPs) based on established frameworks like MITRE ATT&CK. Structured hunts often stem from threat intelligence or assumptions about how attackers may target the organization.
- Unstructured hunting: Unstructured hunts begin with the discovery of an indicator of compromise (IoC), such as anomalous login attempts or unusual network traffic, which serves as the catalyst for further investigation.
- Situational hunting: This approach is tailored to specific organizational contexts and risk profiles. It focuses on high-value assets, users, or systems identified as vulnerable based on recent security assessments, threat intelligence, or changes in the environment. Situational hunting helps prioritize resources where threats are most likely to emerge or cause impact.

Threat Hunting: A Step-by-Step Process
Threat hunters operate under the assumption that cyber adversaries have already infiltrated the system. Their goal is to uncover suspicious or abnormal behavior that may signal malicious activity.
Effective cyber threat hunting follows a proactive, three-phase approach, including:
Step 1: Trigger
The process starts with a trigger that points threat hunters to a particular system or part of the network for a closer look.
This trigger might come from advanced detection tools flagging unusual activity that could indicate malicious behavior.
In other cases, a hunt might start with a new hypothesis, such as suspected fileless malware activity.
Step 2: Investigation
During the investigation stage, threat hunters use tools like Endpoint Detection and Response (EDR) to analyze suspicious activity, confirming whether it’s harmless or part of a broader malicious pattern.
Step 3: Resolution
The resolution phase centers on relaying findings to security and ops teams for a swift, informed response.
Insights, whether from real threats or false positives, are also fed into automated systems to improve future detection and minimize manual effort.

Threat Hunting vs. Threat Detection
To build a proactive security posture, it’s essential to understand how threat hunting differs from threat detection.
Let’s break it down with an easy side-by-side look at the differences.
| Aspect | Threat Hunting | Threat Detection |
| Nature | Proactive | Reactive |
| Goal | Uncover unknown or hidden threats | Identify and alert on known threats |
| Driven by | Human analysts and threat intelligence | Automated systems and predefined rules |
| Tools | EDR, threat intel, behavioral analytics | SIEM, IDS/IPS, log monitoring |
| Primary Outcome | Deep threat discovery and improved defenses | Immediate threat alerts and incident response |
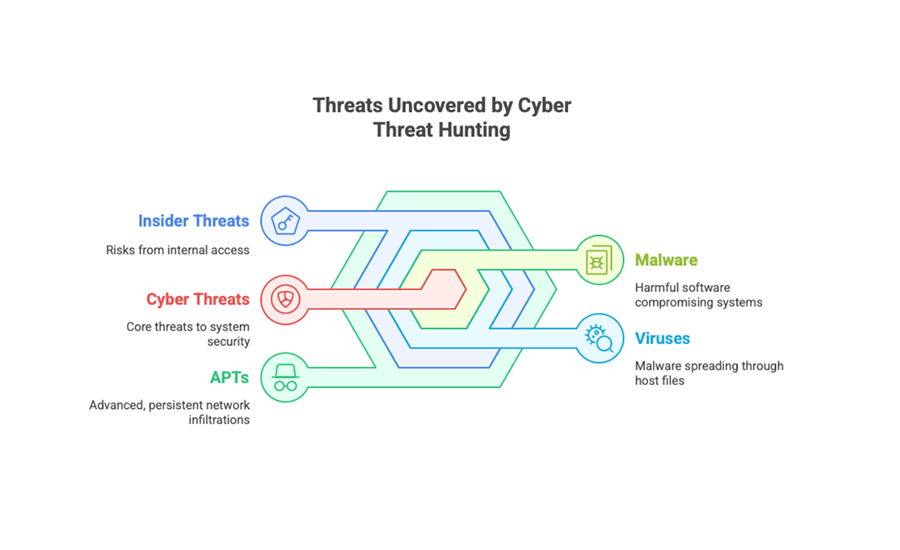
Common Threats Identified by Threat Hunting
Proactive threat hunting helps identify a wide range of threats before they cause damage.
Here are some of the threats they uncover:
1. Malware
Malware, such as ransomware, spyware, adware, trojans, and worms, compromises devices and networks by exploiting vulnerabilities to gain unauthorized access.
2. Viruses
A type of malware that attaches itself to legitimate files or programs, allowing it to execute when the host is run. Viruses can corrupt or delete data and spread to other systems, significantly disrupting operations.
3. Insider Threats
According to Cybersecurity Insiders’ 2024 Insider Threat Report, 83% of organizations experienced at least one insider attack in the past year, which emphasizes the need to monitor trusted users as closely as external threats.
Insider threats stem from individuals with legitimate access who, whether through negligence or intent, compromise the integrity of systems, data, or networks.
4. Advanced Persistent Threats (APTs)
Well-funded, highly skilled attackers launch advanced persistent threats (APTs) by quietly infiltrating networks and keeping long-term access.
They aim to exfiltrate sensitive data, conduct espionage, or set the stage for disruptive attacks like ransomware or sabotage.
5. Social Engineering Attacks
Rather than hacking systems, attackers often target people, tricking them into giving up sensitive information or access.
In 2023, social engineering attacks surged, with scams making up half of all cases worldwide and phishing close behind.
Tactics like phishing, baiting, and scareware prey on human psychology rather than technical flaws.
Cyber Threat Hunting Best Practices
Don’t wait for disaster to strike. Follow these best practices to give your team the edge:
1. Provide Full Visibility
Make sure threat hunters have access to all relevant data, network logs, endpoint activity, cloud environments, and user behavior.
Without full visibility, spotting advanced threats becomes more difficult.
2. Use Integrated Security Tools
Leverage SIEM for centralized logging, EDR to monitor endpoint activity, and XDR to connect insights across layers.
Together, these tools provide the telemetry needed for faster, more informed threat detection and response.
3. Stay Current on Threat Intelligence
Keep your team’s knowledge of attacker TTPs up to date with threat feeds, the MITRE ATT&CK framework, and industry reports.
Relying on outdated assumptions can seriously hinder threat-hunting efforts.
4. Train Staff to Report Anomalies
Educate employees to recognize phishing, unusual system behavior, and access anomalies. User reports can be early indicators of compromise, especially for insider threats.
5. Enforce Vulnerability Management
Regularly scan for and patch known vulnerabilities to reduce attack surfaces and ease the burden on threat hunters.
Explore Threat Hunting & Discovery Services at Forgepath
At Forgepath, our Threat Hunting and Discovery Services are designed to help organizations proactively detect hidden adversaries, uncover stealthy attack patterns, and neutralize threats before they cause harm.
Our team of cybersecurity experts combines advanced analytics, real-time threat intelligence, and leading cybersecurity tools to identify indicators of compromise that traditional defenses often miss.
Whether you’re facing advanced persistent threats, insider risks, or zero-day exploits, our specialists give you the clarity and confidence to take decisive action.
Threat Hunting: FAQs
Do I need specific tools to support threat hunting?
Yes. Threat hunting is more effective with tools like SIEM (security information and event management), EDR (endpoint detection and response), and XDR (extended detection and response).
These tools aggregate and correlate data across environments, making it easier to spot anomalies and uncover hidden threats.
Who should perform threat hunting?
Experienced cybersecurity professionals, such as threat analysts or incident responders, conduct threat hunting by identifying attacker behavior, analyzing TTPs (tactics, techniques, and procedures), and performing forensic investigations.
How often do organizations need to perform threat hunting?
Threat hunting frequency varies based on your organization’s risk exposure, industry standards, and available resources.
Is threat hunting only for large enterprises?
No. While large enterprises often have dedicated in-house teams, small and mid-sized organizations can still benefit from outsourced threat hunting services.
These options make proactive threat detection accessible without the need to build a full-time in-house team.
What outcomes can I expect from a threat hunting engagement?
You can expect the following outcomes:
- Finding hidden or dormant threats
- Enhanced incident response readiness
- Actionable insights to strengthen your overall security posture
![What Is Threat Hunting? [Types, Process & FAQs]](https://forgepath.com/wp-content/uploads/2025/08/threat-hunting-hero-image.jpg)


